What is zero trust?
Always authenticate and authorise based on all available data points.
Limit user access with Just-In-Time and Just-Enough-Access (JIT/ JEA), risk-based adaptive policies, and data protection.
Minimise blast radius and segment access. Verify end-to-end encryption and use analytics to get visibility, drive threat detection, and improve defences.
Verify explicity
Use least privilege access
Assume breach
The Problem
Implicit or explicit trust
- Security is the opposite of productivity.
- All attacks can be prevented.
- Network security perimeter will keep attackers out.
- Passwords are strong enough.
- IT Admins are safe.
- IT Infrastructure is safe.
- Developers always write secure code.
- The software and components we use are secure.
The Solution
Systematically Build & Measure Trust
- Business Enablement - align security to the organization’s mission, priorities, risks, and processes.
- Assume Compromise - continuously reduce blast radius and attack surface through prevention and detection/ response/recovery.
- Shift to Asset-Centric Security Strategy - revisit how to do access control, security operations, infrastructure and development security, and more.
- Explicitly Validate Account Security - require MFA and analyze all user sessions with behaviour analytics, threat intelligence, and more.
- Plan and Execute Privileged Access Strategy - establish security of accounts, workstations, and other privileged entities (aka.ms/spa).
- Validate Infrastructure Integrity - explicitly validate trust of operating systems, applications, services accounts, and more.
- Integrate Security into Development Process - security education, issue detection and mitigation, response, and more.
- Supply Chain Security - validate the integrity of software and hardware components from open source. vendors, and others.
What we offer
24/7 Security Team
Utilizing top-tier EDR and CDR technology
Around-the-clock monitoring
In-house response and intervention services
Comprehensive forensics, malware analysis, and reporting (RCA)

Expert advice
In-depth cyber reviews and attack surface analysis
Prioritized security recommendations
Proactive vulnerability and threat hunting
Security awareness programs

Device Management
Firewall, and data governance all on one easy-to-manage endpoint agent, eliminating agent conflicts
Modules inform each other through a shared data engine, eliminating the need for integration and improving security posture
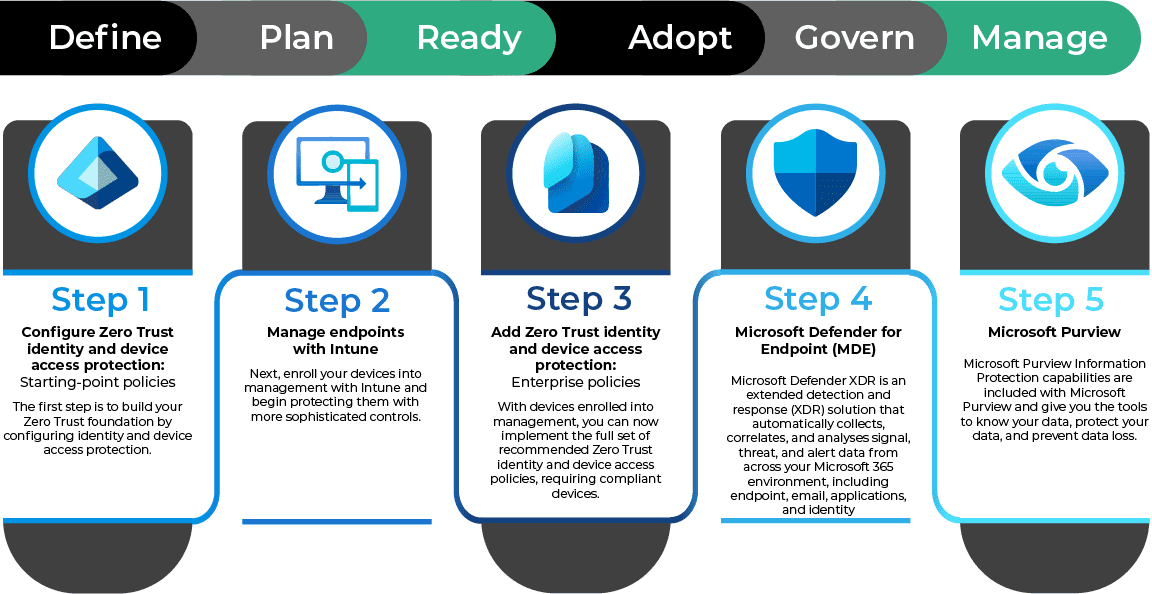
Five steps to apply Zero Trust
Top-Tier Security Tailored for You
Zero Trust is a security framework that operates on the principle of "never trust, always verify," meaning no user, device, or application is inherently trusted, and access to resources is granted only after rigorous authentication and authorization, regardless of location.

Curious about security and integrated protection?

Secure, Provactive managed services
DDS also offers comprehensive consulting services that help organizations navigate the complexities of modern IT landscapes. Our team of experienced professionals excels at identifying opportunities for innovation and transformation, assisting clients in leveraging cloud technologies to enhance their business operations.
Whether it’s optimizing existing infrastructure or developing tailored strategies for digital growth, we guide our clients through every step of their technology journey.
Contact us for a consultation or a tailored services quote
Let’s talk about how we can manage your IT — so you can manage your business.
