Dirac Delta Systems offers Zero Trust for your business
What is Zero Trust?
Zero Trust is a security framework that assumes no user or device is trustworthy by default, requiring continuous verification and strict access controls to protect data and systems.
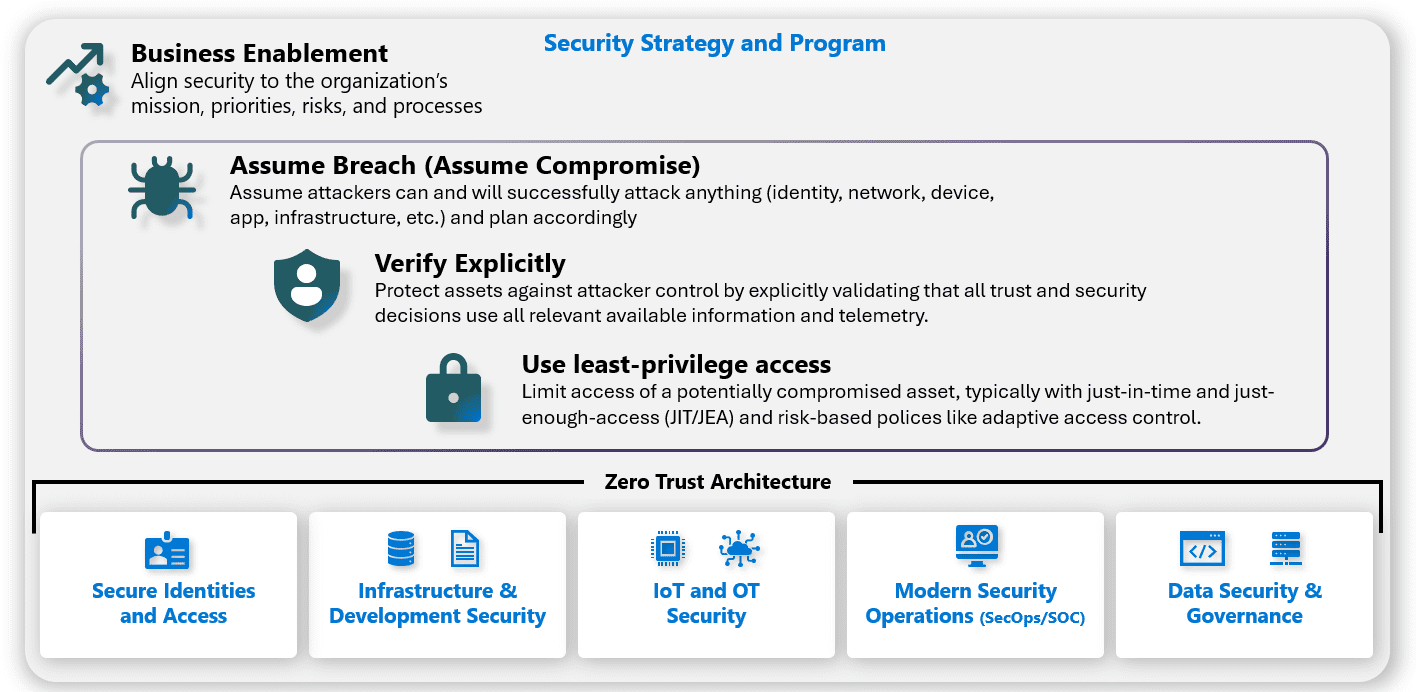
We follow Microsoft Zero Trust Security Principles
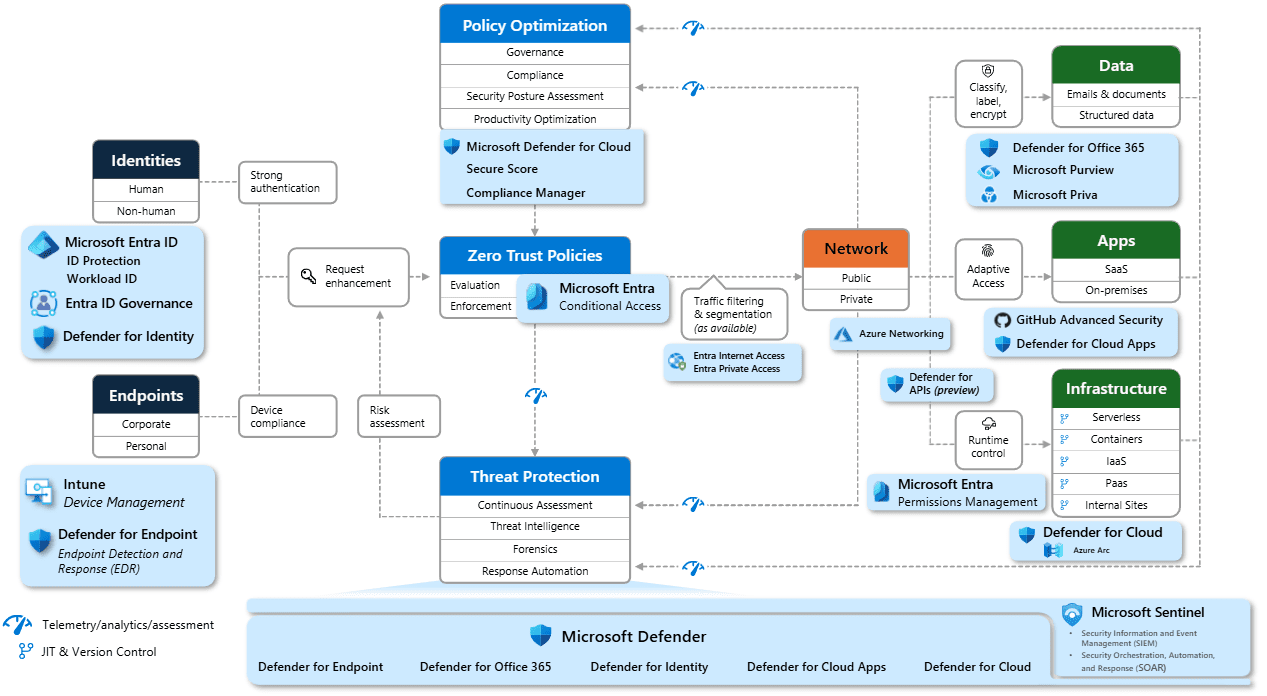
We use Microsoft Zero Trust Architecture
Founded on Microsoft Cybersecurity Reference Architecture (MCRA)

Why are we having a Zero Trust conversation?
Keep assets away from attackers
IT security is complex
- Many devices, users, and connections
“Trusted network” security strategy
- Initial attacks were network-based
- Seemingly simple and economical
- Accepted lower security within the network
Assets increasingly leave the network
- BYOD, WFH, Mobile, and SaaS
Attackers shift to identity attacks
- Phishing and credential theft
- Security teams ofare ten overwhelmed
Goal: Zero Assumed Trust
Reduce risk by finding and removing implicit assumptions of trust
THE PROBLEM
False Assumptions: of implicit or explicit trust
- Security is the opposite of productivity.
- All attacks can be prevented.
- Network security perimeter will keep attackers out.
- Passwords are strong enough.
- IT Admins are safe.
- IT Infrastructure is safe.
- Developers always write secure code.
- The software and components we use are secure.
THE SOLUTION
Zero Trust Mitigation: Systematically Build & Measure Trust
- Business Enablement - align security to the organization’s mission, priorities, risks, and processes.
- Assume Compromise - continuously reduce blast radius and attack surface through prevention and detection/ response/recovery.
- Shift to Asset-Centric Security Strategy - revisit how to do access control, security operations, infrastructure and development security, and more.
- Explicitly Validate Account Security - require MFA and analyze all user sessions with behaviour analytics, threat intelligence, and more.
- Plan and Execute Privileged Access Strategy - establish security of accounts, workstations, and other privileged entities (aka.ms/spa).
- Validate Infrastructure Integrity - explicitly validate trust of operating systems, applications, services accounts, and more.
- Integrate Security into Development Process - security education, issue detection and mitigation, response, and more.
- Supply Chain Security - validate the integrity of software and hardware components from open source. vendors, and others.
Security Modernization with Zero Trust Principles
What is Zero Trust?
Zero Trust is a security strategy. It is not a product or a service, but an approach in designing and implementing the following set of security principles:
Verify explicitly
Always authenticate and authorize based on all available data points.
Use least privilege access
Limit user access with Just-In-Time and Just-Enough-Access (JIT/JEA), risk-based adaptive policies, and data protection.
Assume breach
Minimize blast radius and segment access. Verify end-to-end encryption and use analytics to get visibility, drive threat detection, and improve defences.
Zero Trust architecture
Microsoft Resources: Zero Trust for Small Businesses
Zero Trust deployment guidance and resources for customers and partners working with Microsoft 365 Business Premium. These resources help you realize the principles of Zero Trust:
Zero Trust Adoption Framework

Adopting a Zero Trust approach requires buy-in across the C-suite.
A formal security strategy aligned to business outcomes.
Build a business case focused on the outcomes most closely aligned with your organization’s risks and strategic goals.
Track and measure the success of your deployment.


Microsoft 365 Business Premium Partner Playbook

Practical Guide to Deploying Microsoft 365 Business Premium.

Learn how to successfully land the value from Microsoft 365 Business Premium.

Microsoft 365 Business License Comparison.

Presentation Resources for deployment planning.
Enhancing security with Microsoft 365 Business: checklist

Focus on strategic objectives before deployment.
Reference URLs for technical implementation steps.


Practical guide to security using Microsoft 365 Business

Develop your deployment strategy using a formal template

A formal security strategy aligned to business outcomes.

Showcase measurable success to stakeholders as the project proceeds.
Contact us for a consultation or tailored quote
Let’s talk about how we can manage your IT — so you can manage your business.
















